Expert Insights into Managed Data Protection for Modern Businesses
Exactly How Managed Data Defense Safeguards Your Organization From Cyber Threats
In an era where cyber dangers are increasingly sophisticated, the importance of managed data security can not be overemphasized. Organizations that execute extensive safety and security procedures-- such as information encryption, gain access to controls, and continual tracking-- are better outfitted to safeguard their sensitive information.

Recognizing Managed Data Defense
Managed information defense is an important part of contemporary cybersecurity techniques, with approximately 60% of companies selecting such services to safeguard their important info properties. This strategy entails outsourcing data protection obligations to customized provider, permitting companies to concentrate on their core company features while ensuring durable safety steps remain in area.
The significance of managed data security exists in its ability to provide extensive remedies that include data backup, recovery, and threat discovery. By leveraging advanced modern technologies and proficiency, took care of provider (MSPs) can execute aggressive steps that reduce threats related to information violations, ransomware strikes, and various other cyber hazards. Such solutions are made to be scalable, suiting the developing requirements of organizations as they adjust and expand to brand-new obstacles.
Furthermore, managed information protection promotes compliance with governing demands, as MSPs often remain abreast of the most current market requirements and practices (Managed Data Protection). This not only improves the safety posture of a company yet additionally imparts self-confidence amongst stakeholders relating to the stability and discretion of their data. Eventually, comprehending taken care of data protection is important for companies seeking to fortify their defenses against the ever-changing landscape of cyber threats
Trick Elements of Data Protection
Effective data security approaches commonly encompass a number of vital elements that operate in tandem to guard delicate information. Primarily, data security is crucial; it transforms readable information right into an unreadable style, ensuring that even if unauthorized gain access to occurs, the information stays safeguarded.
Gain access to control is another critical component, allowing companies to restrict information accessibility to licensed workers only. This lessens the risk of inner breaches and enhances responsibility. Additionally, normal data back-ups are important to guarantee that information can be recovered in the event of information loss or corruption, whether due to cyberattacks or unintended removal.
Following, a durable safety policy ought to be developed to describe treatments for data handling, storage space, and sharing. This policy ought to be frequently upgraded to adjust to evolving dangers. Additionally, constant tracking and bookkeeping of information systems can identify anomalies and potential breaches in real-time, assisting in speedy reactions to dangers.
Advantages of Managed Provider

In addition, handled solutions promote proactive tracking and hazard detection. MSPs utilize sophisticated modern technologies and tools to continuously check systems, making sure that anomalies are identified and attended to prior to they rise into severe issues. This positive method not only reduces action times yet additionally mitigates the potential impact of cyber events.
Cost-effectiveness is another key advantage. By outsourcing information security to an MSP, organizations can avoid the substantial prices related to in-house staffing, training, and innovation financial investments. This enables business to allocate sources a lot more effectively while still taking advantage of top-tier protection services.
Compliance and Regulatory Assurance
Ensuring conformity with industry laws and criteria is an important element of data protection that companies can not neglect. Regulative frameworks, such as GDPR, HIPAA, and PCI DSS, impose rigorous needs on exactly how companies manage and safeguard sensitive information. Non-compliance can lead to severe fines, reputational damages, and loss of customer trust fund.
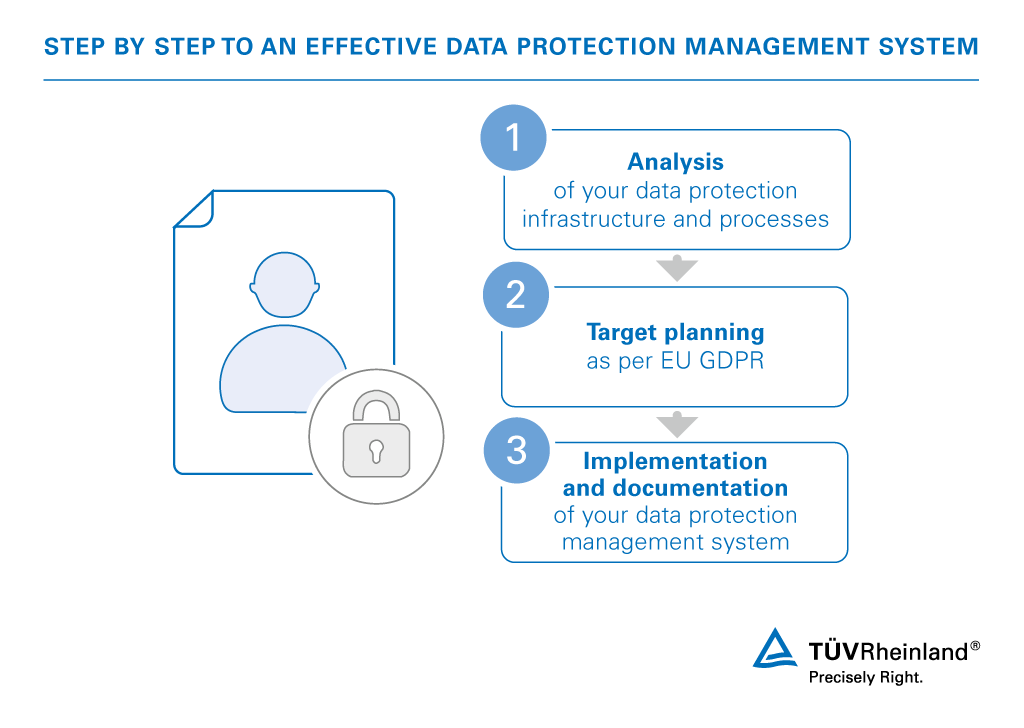
Managed information security services aid helpful hints organizations browse the complicated landscape of compliance by implementing durable security procedures tailored to meet certain regulative needs. These solutions use methodical techniques to data encryption, access controls, and routine audits, guaranteeing that all procedures straighten with legal obligations. By leveraging these handled solutions, organizations can maintain continual oversight of their data defense techniques, making certain that they adjust to progressing regulations.
Furthermore, thorough reporting and documents offered by taken care of data security services function as valuable tools throughout conformity audits. These records demonstrate adherence to developed procedures and criteria, offering guarantee to stakeholders and governing bodies. Inevitably, buying taken care of information security not only fortifies a company's cybersecurity stance yet also imparts self-confidence that it is devoted to maintaining compliance and regulative guarantee in an increasingly intricate electronic landscape.
Selecting the Right Supplier
Picking the right managed data defense provider is important for companies intending to improve their cybersecurity frameworks. The first step in this process is to assess the company's knowledge and experience in the area of information security. Search for a provider with a proven performance history of effectively protecting organizations versus numerous cyber dangers, along with knowledge with industry-specific regulations and compliance needs.
In addition, examine the variety of solutions provided. A detailed provider will provide not only backup and recuperation options but likewise proactive threat discovery, risk assessment, and case action abilities. It is vital to make certain that the provider uses sophisticated technologies, consisting of file encryption and multi-factor verification, to secure delicate data.
A responsive support team can substantially impact your organization's capability to recoup from incidents quickly. By thoroughly analyzing these elements, companies can make an educated choice and choose a carrier that aligns with their cybersecurity objectives, ultimately enhancing their this page protection versus cyber dangers.
Conclusion
To conclude, handled information security offers as an essential defense against cyber hazards by utilizing durable safety steps, specific expertise, and progressed technologies. The combination of thorough strategies such as data file encryption, gain access to controls, and constant tracking not only reduces dangers but likewise makes sure compliance with regulative standards. By contracting out these services, companies can improve their security visit homepage structures, promoting rapid recuperation from information loss and promoting confidence amongst stakeholders in the face of ever-evolving cyber dangers.
In an age where cyber threats are increasingly sophisticated, the value of taken care of data protection can not be overstated.The significance of handled data defense lies in its ability to use detailed services that consist of data back-up, healing, and threat discovery. Inevitably, recognizing taken care of information security is critical for organizations looking for to fortify their defenses versus the ever-changing landscape of cyber threats.
In final thought, handled information security serves as an essential protection versus cyber hazards by utilizing durable security measures, specialized competence, and progressed technologies. Managed Data Protection.